That’s not what “private” means. If they have both keys, the wording “might be able to” is at best extremely misleading.
I mean, no yes man would enforce the fascist technocrat’ order of reading all those messages. You know, the same technocrat who bought Twitter with Saudi money to cripple resistance movements and steer the public toward the alt right. The one with a thing for eugenics.
If anyone except you has the private key, then your private messages are not private.
To extend this, that includes YOU giving your key to another application to decrypt those messages.
For example if you use an app or browser extension, that app or browser extension has access to that key. Additionally the browser itself or operating system had access to the key.
Now they may be fully audited. They may have a great reputation. You may trust them. But they are part of the decryption (and if sending encryption) process.
It’s a chain of trust, you have to trust the whole chain.
It’s a chain of trust, you have to trust the whole chain.
Including the entire other side of the conversation. E2EE in a group chat still exposes the group chat if one participant shares their own key (or the chats themselves) with something insecure. Obviously any participant can copy and paste things, archive/log/screenshot things. It can all be automated, too.
Take, for example, iMessage. We have pretty good confidence that Apple can’t read your chats when you have configured it correctly: E2EE, no iCloud archiving of the chats, no backups of the keys. But do you trust that the other side of the conversation has done the exact same thing correctly?
Or take for example the stupid case of senior American military officials accidentally adding a prominent journalist to their war plans signal chat. It’s not a technical failure of signal’s encryption, but a mistake by one of the participants inviting the wrong person, who then published the chat to the world.
Are you so sure Apple doesn’t have your keys? How are they migrating the keys to your new device? It’s all closed source
That’s not “probably”. If they have the key they straight up have access. The key to my house can’t just probably unlock the door.
And yet people still keep using Twatter like it’s the only thing that has ever existed since the dawn of the internet. At this point, you deserve to get wrecked for still using this platform.
Which effectively means the messages aren’t encrypted. Cool.
It also effectively means they are reading those messages.
I mean they’re encrypted in transit. They’re just not end to end encrypted.
Do not look at all those (proprietary) E2EE definitions to closely - you might find several that define TLS as end to end…
I mean TLS is also encryption in transit, it’s in the name. And it would sorta be end to end if you’re terminating TLS at the end you’re trying to talk to.
Thats the problem. Say, I’m offering you a cloud drive and tell you “your data is end to end encrypted”. You sync data from your PC to my server and from my server to your mobile phone. Would that mean
- That everything between your devices is encrypted (=I can’t see what you’re saving, neither can “the state”, hackers,…)or
- That your data is encrypted in transit, but is saved unencrypted on my server (which means everyone with access to my server can see your data) or
- It’s encrypted in transit and also on my server, but the keys are also ony server, so that everyone with access to my server can in theory decrypt everything and access everything?
1 is what you want, 2 and 3 are often what you get…
It’s not that I disagree with you on principle, I think you’re just kinda mixing up scenarios here, and the purpose of E2EE. E2EE refers to in transit data specifically. #1 should never be where your mind goes because E2EE does not imply your data will be encrypted at rest at the destination, that’s not what it’s for. E2EE is a critical factor when the untrusted facilitator party is between you and your intended recipient, not the recipient themselves.
Like in your scenario of a “cloud drive”, E2EE would not be a selling point of that service. The term you’re looking for in that scenario is “zero access encryption”.
Like you’re correct that E2EE does not imply that data stored in the cloud is encrypted at rest, but that’s because it isn’t meant to. Like this isn’t a dirty marketing trick. E2EE just needs to do what it says on the tin, which this X chat does not because they in order for it to be E2EE, it needs to be the case that only the recipient can decrypt it.
The third paragraph contradicts your other point. You define E2EE in two wildly different ways.
The chat messages are most likely stored on an intermediary server, which would qualify for the same loophole you pointed out in the cloud storage example.
No it doesn’t, and I defined E2EE exactly one way. E2EE stands for “End to end encryption”, which means it’s encrypted at one end, decrypted at the other end, and not in the middle.
It doesn’t matter if they store a copy of your message on an intermediary server, the keyword there is intermediary. They are not the recipient, so they should not have the ability to decrypt the content of the message, only the recipient should. If they are able to decrypt your message, despite not being the recipient, it’s not E2EE.
A cloud drive is an entirely different case because the cloud drive is not an intermediary. They literally are the second E in E2EE. A cloud drive can have the ability to decrypt your data and still be E2EE because they are the recipient. You both seem to be under the impression that a cloud drive is an “intermediary” between your devices but it’s not. It’s a destination.
To explain it a bit simpler, imagine we’re in elementary school sitting at our desks and you’re sitting two desks away from me with one person between us:
E2EE = I encrypt my note with a simple cipher that I shared with you and only you before class. I pass my note to the kid between us to pass to you. He can’t read the note, and if he writes down a copy of my note before passing it to you it doesn’t matter because he still won’t be able to read it because he’s doesn’t have the cipher because he’s not the recipient, you are. He passes you the note and you can do whatever you want with it, including decrypting it, because you know the cipher. All the E2EE has done is ensured the kid in the middle can’t read the note. It has nothing to do with whether or not you can read the note.
Zero Access Encryption = I encrypt my note with a cipher that only I know. The kid in the middle can’t read this note, and neither can you. Then I use E2EE to encrypt that with a different cipher, the one that you do know, and hand the note to the kid in the middle to hand to you. The kid in the middle can’t read the note, and neither can you.
Stop using fascist things.
Stores, websites, apps, cars, hosting, operating systems, and all other providers of goods/services should be audited by you. You should then ask yourself if you want to give them your money and/or your trust.
I’m trying, but they keep forcing it into devices I already own and even with turning it off in the settings sometimes it gets turned back on during updates. At least avoiding the X/shitter bot is easy enough, but the rest are just as invasive.
Out of curiosity what devices are giving you these issues? I may know of some alternatives depending.
Anything with a web browser. Work computers. Phone. Have to turn off the AI crap on all of those manually after they were added in updates.
Don’t really believe turning off the settings keeps them from farming data either, since they constantly lie about what data they collect and use for training.
For web browser’s, check librewolf or brave, I would lean further towards librewolf just because it’s oss which is something I value.
For search engines, we’re in a weird spot right now because Microsoft is restricting the use of Bing’s search API, but duck duck go is good, and ecosia as well, but they both may be in a rough spot soon.
Work computer you can’t do much other than ask your supervisor to ask about moving away from ai stuff, all you can do directly is limit your personal information on your work station.
For phones, If you have apple, sorry, if not, you could look into changing the operating system on it to something like e/os or graphene os, they are both operating systems that are focused on privacy and security.
If you need anymore information about my recommendations, I am happy to help.
On my desktop (windiws) I use Libre wolf for most things, but Firefox for YouTube because I’m signed in with my Google account for subs and stuff. I use FF for only youtube on the PC though, and yeah open source few.
I use Firefox on my phone as I don’t think Librewolf has a mobile version.
I use duck duck on all the browsers, but it is going downhill.
At some point I will switch desktop to Linux, just haven’t come up with a plan for backing up data to do a smooth transition. Keep putting it off when life stuff come up.
Xchat is an irc client though.
The one true XChat
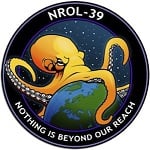
inb4 the logo looks like this:

Nostalgia intensifies
This is the first thing that came to mind. I used that for ao many years, then went on to Hexchat.
I’m surprised nobody posted the surprised_pikachu.gif yet.
Yes and? Do people who use X really care about privacy. Everyone who even remotely cared already jumped ship and moved on to matrix, signal, Simplex etc.
And im not even mentioning the fact X is owned by a psychopath. But hey let’s pretend they care about your privacy.
deleted by creator
Enshittification continues